Windows January update problems - KB5009557, KB5009546, KB5009555
I know what you are thinking. Windows post, on this blog? Considering how important it is, let's leave it at that.
About a week ago as the new Windows updates for January arrived, so did new problems for system administrators, and users for that matter.
Depending on the OS, Windows Server 2012R2, 2019, 2022, you probably got one of the patches from the title: KB5009557, KB5009546, KB5009555.
Issues with those updates translate to the following:
- Boot loops on the server after installing the security updates. Post-installation of the security update, your servers are unable to boot properly. Uninstalling the patch resolves the boot loop issue on the affected servers. The issue, chiefly, affects domain controllers.
- Hyper VM V may break on the server. This may cause the virtual servers to fail on the server. Break in the virtualization layer can be resolved by uninstalling the security update KB5009557.
- ReFS volumes, internal as well as external, may turn RAW after installing the security update. Uninstalling the patch resolves the issue and the ReFS volume drives regain their original state.
- VPN connections, L2TP, and IPSEC tunnels may fail after installing the patch on the servers.
- LDAP bindings may fail on the servers.
So why is this important, and why am I writing an article about it? Well, the point is that if you try and add your Synology NAS into Active Directory backed up by servers with those patches, you will, get this, reboot the servers. Not bad right?
So once you start adding your NAS using the procedure it will be all well until DSM starts talking to your domain.
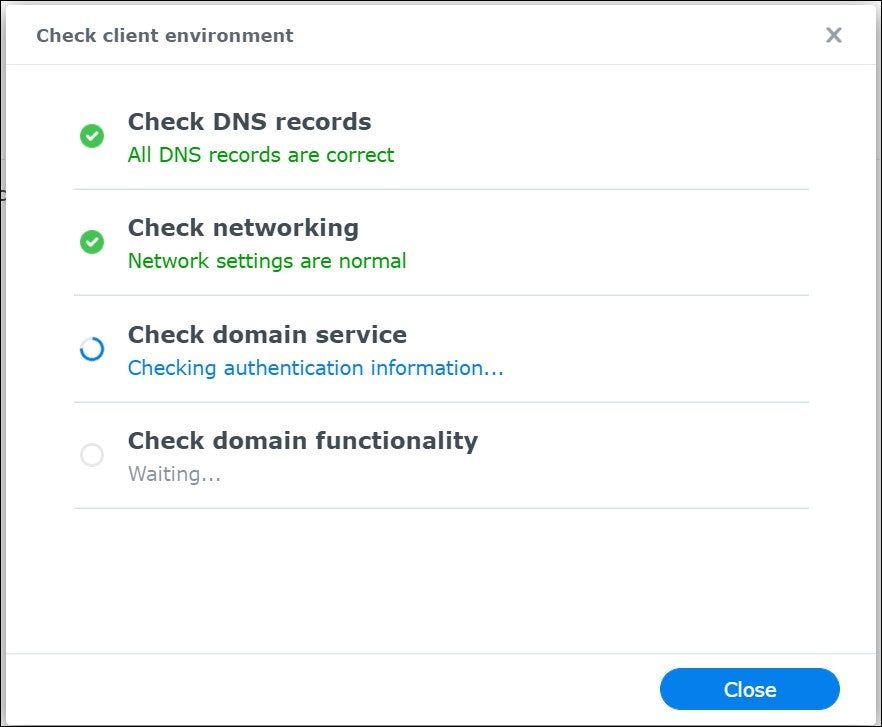
But then on the server-side, this happens.

At the same time, DSM reports the following.
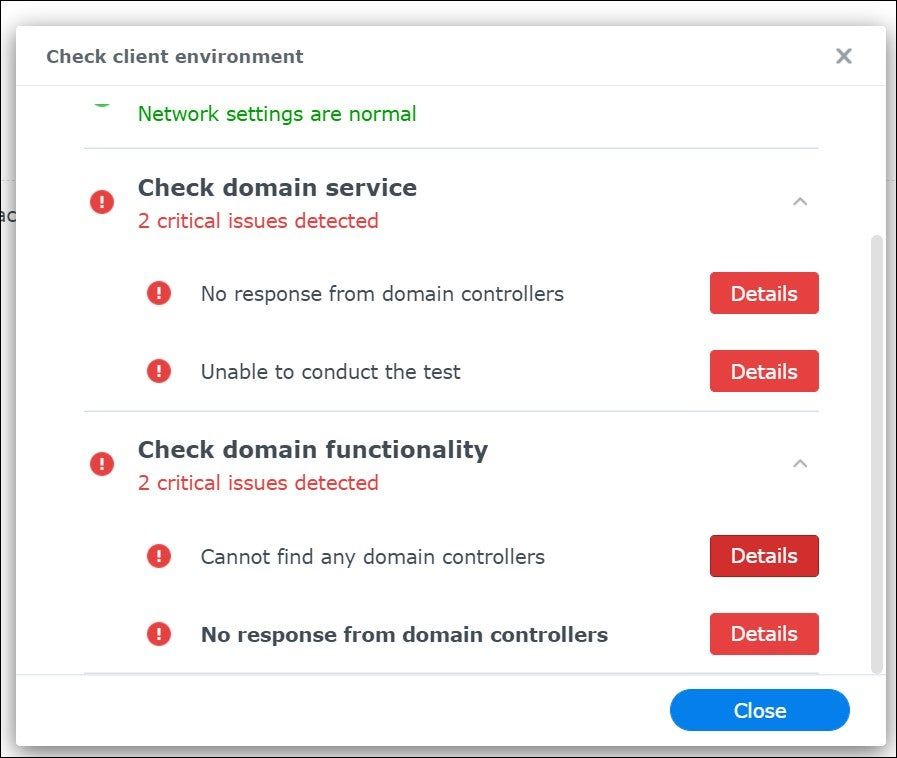
To make matter worse, your server will loop-reboot until you disjoin the NAS from the domain.
So, before you start looking for reasons in all the wrong places, roll back your servers, and hold off with January patches for now. Thank you Microsoft (again).





