Synology DSM 7.1.1-42962

Version: 7.1.1-42962 Update 6
(2023-06-05)
Important notes
- Your Synology NAS may not notify you of this DSM update because of the following reasons. If you want to update your DSM to this version now, please click here to update it manually.
- Your DSM is working fine without having to update. The system evaluates service statuses and system settings to determine whether it needs to update to this version.
- Depending on your Synology NAS model, this update will restart the device.
Fixed Issues
- Fixed an issue where, if the space reclamation process had encountered a heavy workload, the file system may be unable to mount after a system restart.
- Fixed an issue where the system was unable to display an expansion unit's storage pools if the unit had not been properly connected during a restart.
- Fixed an issue where the S.M.A.R.T. test results of NVMe SSDs could not be displayed.
Notes:
- This version is released in a staged rollout.
Version: 7.1.1-42962 Update 5
(2023-04-12)
Important notes
- Your Synology NAS may not notify you of this DSM update because of the following reasons. If you want to update your DSM to this version now, please click here to update it manually.
- Your DSM is working fine without having to update. The system evaluates service statuses and system settings to determine whether it needs to update to this version.
- Depending on your Synology NAS model, this update will restart the device.
- Users of HD6500 can now create a Btrfs volume of up to 1 PB. This update automatically converts existing volumes that use the Btrfs (Peta Volume) file system to Btrfs. However, to create a volume larger than 200 TB, a RAID 6 storage pool and at least 64 GB of system memory are still required.
What’s New
- Updated OpenSSL to version 1.1.1t to fix multiple security vulnerabilities (CVE-2023-0286, CVE-2023-0215, CVE-2022-4450, CVE-2022-4304).
Fixed Issues
- Fixed an issue where users couldn't access DSM via the Bonjour service.
- Fixed stability issue of QuickConnect connections.
- Fixed an issue where Synology mobile apps remained signed in after users ended all connections following a password change.
- Fixed an issue of space reclamation not running according to the set schedule.
- Fixed a display issue concerning the notification about incompatible network interface cards.
Version: 7.1.1-42962 Update 4
(2023-02-06)
Important notes
- Your Synology NAS may not notify you of this DSM update because of the following reasons. If you want to update your DSM to this version now, please click here to update it manually.
- Your DSM is working fine without having to update. The system evaluates service statuses and system settings to determine whether it needs to update to this version.
- Depending on your Synology NAS model, this update will restart the device.
Compatibility & Installation
- The following drives will be updated automatically to the latest firmware version to fix an unexpected issue that may occur during repair or other read/write operations: HAT5300-4T (firmware version 1401 and 1402), HAT5300-16T (firmware version 1401), HAT5310-8T (firmware version 1401), and HAS5300-16T (firmware version 1401).
What’s New
- Added support for E10G22-T1-Mini with an alternative source of hardware components.
Fixed Issues
- Fixed an issue where drives added to a RAID Group in a Synology High Availability cluster were not allocated correctly between RAID arrays.
Version: 7.1.1-42962 Update 3
(2022-12-08)
Important notes
- Your Synology NAS may not notify you of this DSM update because of the following reasons. If you want to update your DSM to this version now, please click here to update it manually.
- Your DSM is working fine without having to update. The system evaluates service statuses and system settings to determine whether it needs to update to this version.
- Depending on your Synology NAS model, this update will restart the device.
Fixed Issues
- Fixed multiple security vulnerabilities. (Synology-SA-22:23)
Notes:
- This version is released in a staged rollout.
Version: 7.1.1-42962 Update 2
(2022-10-20)
Important notes
- Your Synology NAS may not notify you of this DSM update because of the following reasons. If you want to update your DSM to this version now, please click here to update it manually.
- Your DSM is working fine without having to update. The system evaluates service statuses and system settings to determine whether it needs to update to this version.
- Depending on your Synology NAS model, this update will restart the device.
What’s New
- When users select Outlook as the system notification service provider, they will need to sign in with OAuth 2.0, which is a safer authentication method. Previously configured Outlook accounts will be migrated to "Custom SMTP server". We strongly recommend re-configuring the settings for authentication to ensure your Outlook account security.
Fixed Issues
- Fixed an issue where performing file system checks on ext4 volumes would stop the quota settings on DSM from functioning.
- Fixed an issue where after HDD migration, users couldn't properly mount the SSD caches that weren't migrated to the new device.
- Fixed an issue where Universal Search couldn't find the data in shared folders on volumes that were created on DSM 7.1.1.
- Fixed an issue where users couldn't access DSM from certain devices.
- Fixed an issue where users couldn't access DSM via the Bonjour service.
- Fixed an issue where the E10G18-T1 network card couldn't be detected on the passive server when creating a Synology High Availability cluster with RC18015xs+.
- Fixed an issue where models with the AMD Ryzen V1000 CPU platform couldn't adjust the fan speed automatically after a system reboot.
- Fixed multiple security vulnerabilities regarding Out-of-Band (OOB). (Synology-SA-22:17)
Version: 7.1.1-42962 Update 1
(2022-09-22)
Important notes
- Your Synology NAS may not notify you of this DSM update because of the following reasons. If you want to update your DSM to this version now, please click here to update it manually.
- Your DSM is working fine without having to update. The system evaluates service statuses and system settings to determine whether it needs to update to this version.
- Depending on your Synology NAS model, this update will restart the device.
Fixed Issues
- Fixed an issue where users might not be able to change the desktop background.
- Fixed an issue where volumes might become read-only due to data block allocation problems.
- Fixed an issue where LUN backup tasks in Hyper Backup might fail after updating DSM 7.1.1.
Today we got a new version of DSM, 7.1.1-42962. Following last month's release candidate of this version, now we got the official one out.
It will be released in a staged rollout, so if you want it now, you need to do it manually using the Download Center page on the Synology website.
This is a massive security release so if your production system is running on DSM 7.1, it would be highly advisable to update to this patch level.
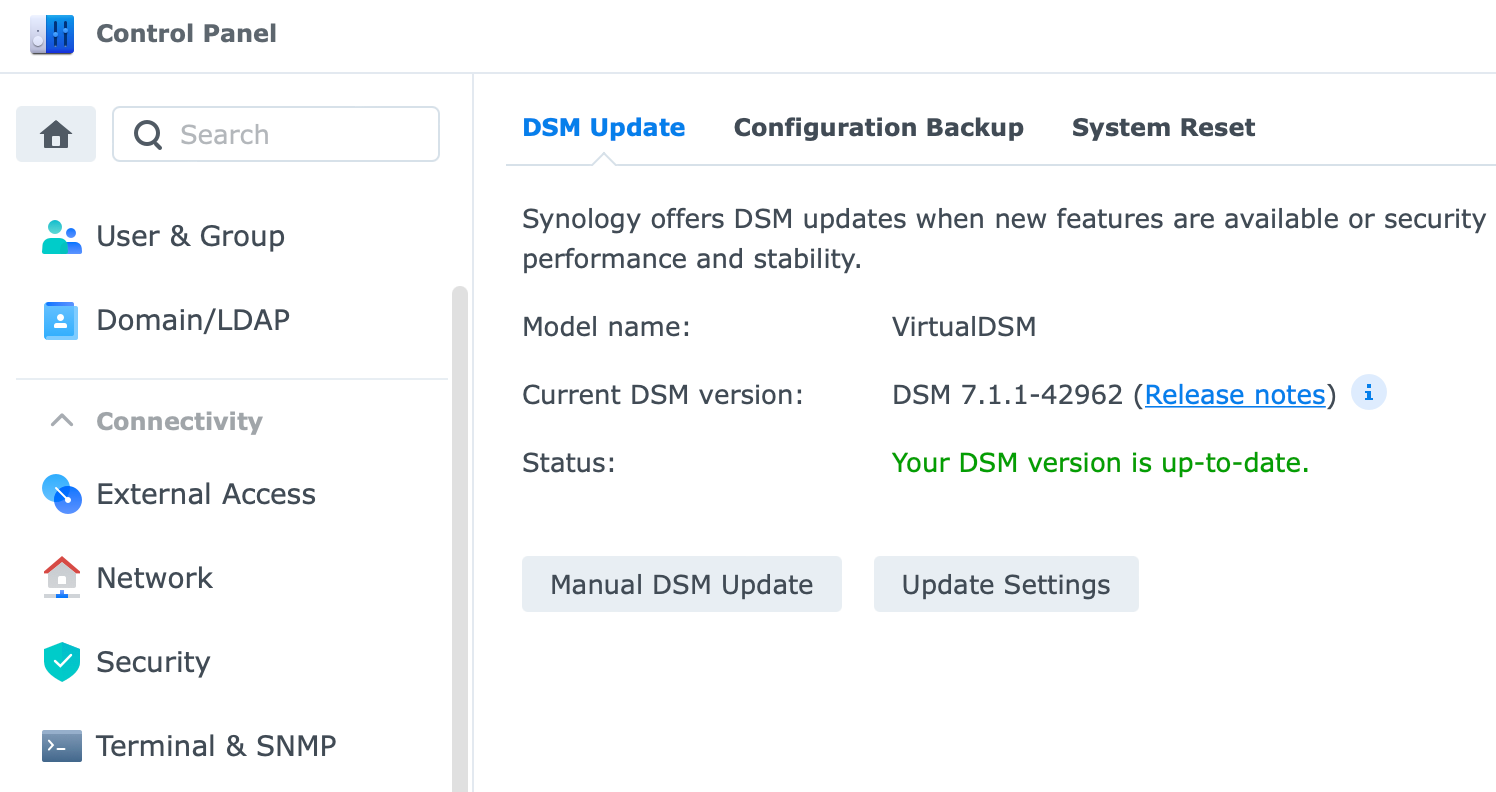
Version: 7.1.1-42962
(2022-09-05)
Important Notes
- Starting from this version, the bad sector count column will not be displayed along with hard drive information. Users should go to each drive's Health Info > History to view its complete bad sector information. To determine whether bad sectors are affecting the drive, see if there's a significant increase in the number of bad sectors over time.
- Adjusted how the system calculates the estimated lifespan for M.2 NVMe SSDs to provide a more accurate estimation.
- Support for AAC encoded audio is widespread across end devices like smartphones, tablets, computers, and the majority of other media playback devices. The need for AAC transcoding to achieve better compatibility has significantly diminished and will be removed starting with DSM 7.1.1.
- Surveillance Station must be updated to version 9.0.1- 7673 or above to be compatible with this update.
What’s New
- Added support for recipient profiles for email notifications, allowing users to add multiple email addresses under each profile and customize rules for the profiles.
- Users can now enable the quota setting for shared folders that are located on volumes with data deduplication enabled.
- Added support for RAID arrays with 16 and 20 hard drives when creating RAID groups.
- Supports checking the 2-factor authentication status of user accounts at Control Panel > User & Group > Users.
- Added support for SR-IOV on the following the Synology network interface cards: E10G21-F2, E25G21-F2.
Fixed Issues
- Fixed an issue where the "Enable UID/GID shifting" setting would be deactivated after modifying the time interval for updating the user/group list on an LDAP client.
- Fixed multiple security vulnerabilities regarding CIFS-utils (CVE-2022-27239, CVE-2022-29869).
- Fixed a security vulnerability regarding OpenLDAP (CVE-2022-29155).
- Fixed a security vulnerability regarding cURL (CVE-2022-22576).
- Fixed a security vulnerability regarding Zlib (CVE-2018-25032).
- Fixed a security vulnerability regarding Freetype (CVE-2022-27406).
- Fixed multiple security vulnerabilities regarding 802.1X (CVE-2021-30004, CVE-2021-30266).
- Fixed multiple security vulnerabilities regarding GNU C Library(CVE-2021-43396, CVE-2022-23218, CVE-2022-23219).
- Fixed multiple security vulnerabilities regarding YAML-cpp (CVE-2018-20573, CVE-2018-20574, CVE-2019-6285).
- Fixed multiple security vulnerabilities regarding Linux Kernel (CVE-2019-11477, CVE-2019-11478, CVE-2019-11479, CVE-2020-12770, CVE-2019-18282, CVE-2019-19527, CVE-2019-19532, CVE-2019-19537, CVE-2021-0605, CVE-2021-3732, CVE-2021-3739, CVE-2021-3753, CVE-2021-4149, CVE-2021-4203, CVE-2021-20317, CVE-2021-20321, CVE-2021-20322, CVE-2021-29154, CVE-2021-29650, CVE-2021-34556, CVE-2021-35477, CVE-2021-39633, CVE-2021-39698, CVE-2021-45868, CVE-2022-0185, CVE-2022-0330, CVE-2022-0617, CVE-2022-0847, CVE-2022-1011, CVE-2022-1048, CVE-2022-1055, CVE-2022-1353, CVE-2022-20008, CVE-2022-27666, CVE-2022-28893, CVE-2022-29582).
- Updated OpenSSL to version 1.1.1o to fix multiple security vulnerabilities (CVE-2022-1292, CVE-2021-3712, CVE-2022-0778).
- Updated libarchive to version 3.6.1 to fix multiple security vulnerabilities (CVE-2021-36976, CVE-2022-26280).
- Updated Mbed-TLS to version 2.28 to fix multiple security vulnerabilities (CVE-2021-44732, CVE-2021-45450, CVE-2021-43666).
- Updated Python to version 3.8.12 to fix multiple security vulnerabilities (CVE-2021-3733, CVE-2021-3737, CVE-2022-0391).
- Updated Redis to version 6.2.7 to fix multiple security vulnerabilities (CVE-2022-24735, CVE-2022-24736).
- Updated ISC DHCP to version 4.4.3 to fix a security vulnerability (CVE-2021-25217).
Quite a long list of vulnerabilities so best not to skip it. I have updated several machines, including some virtual ones, and they all came up with zero issues.